GitHub - vlepilov/wordlist-1: Collection of some common wordlists such as RDP password, user name list, ssh password wordlist for brute force. IP Cameras Default Passwords.
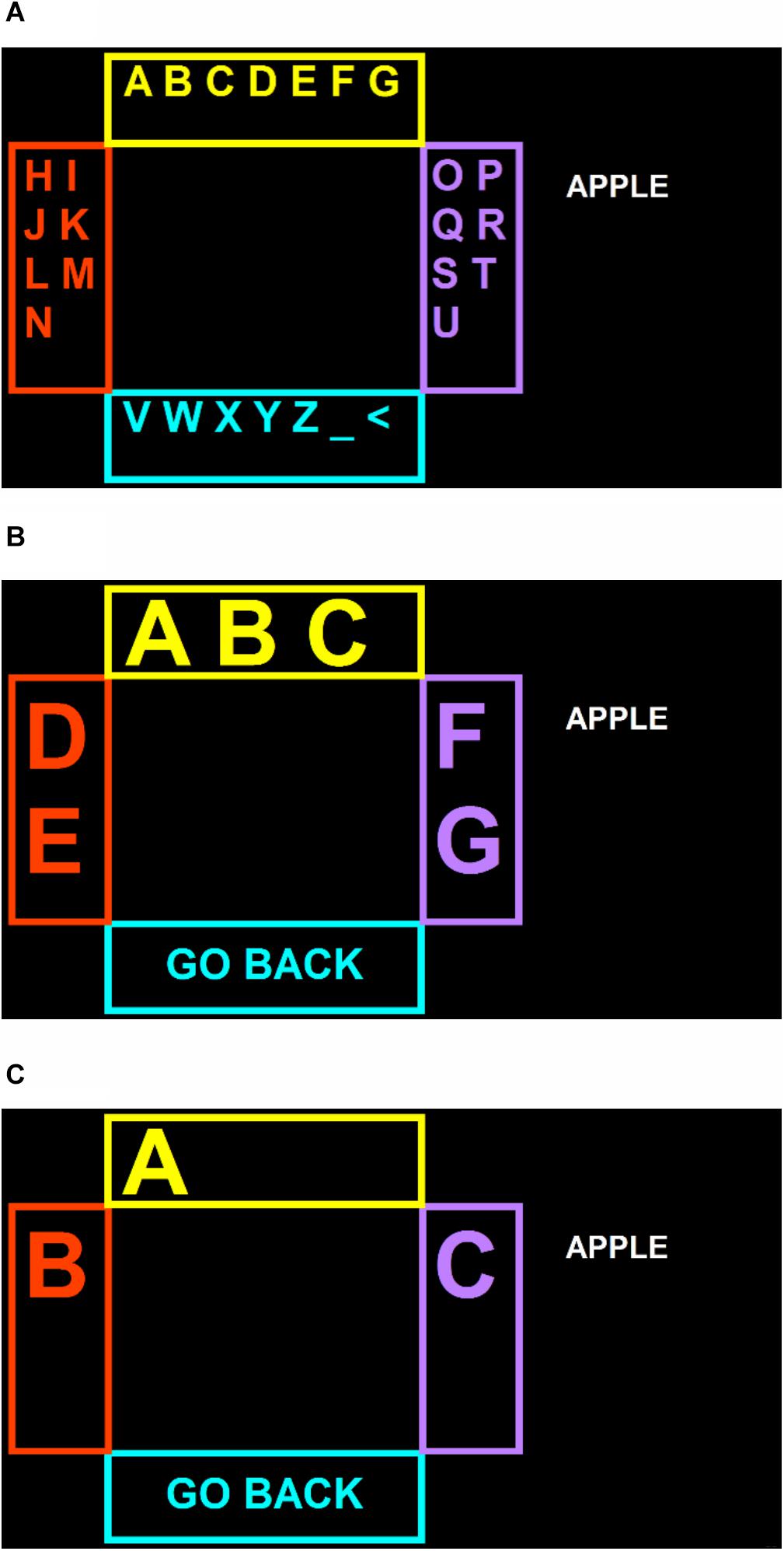
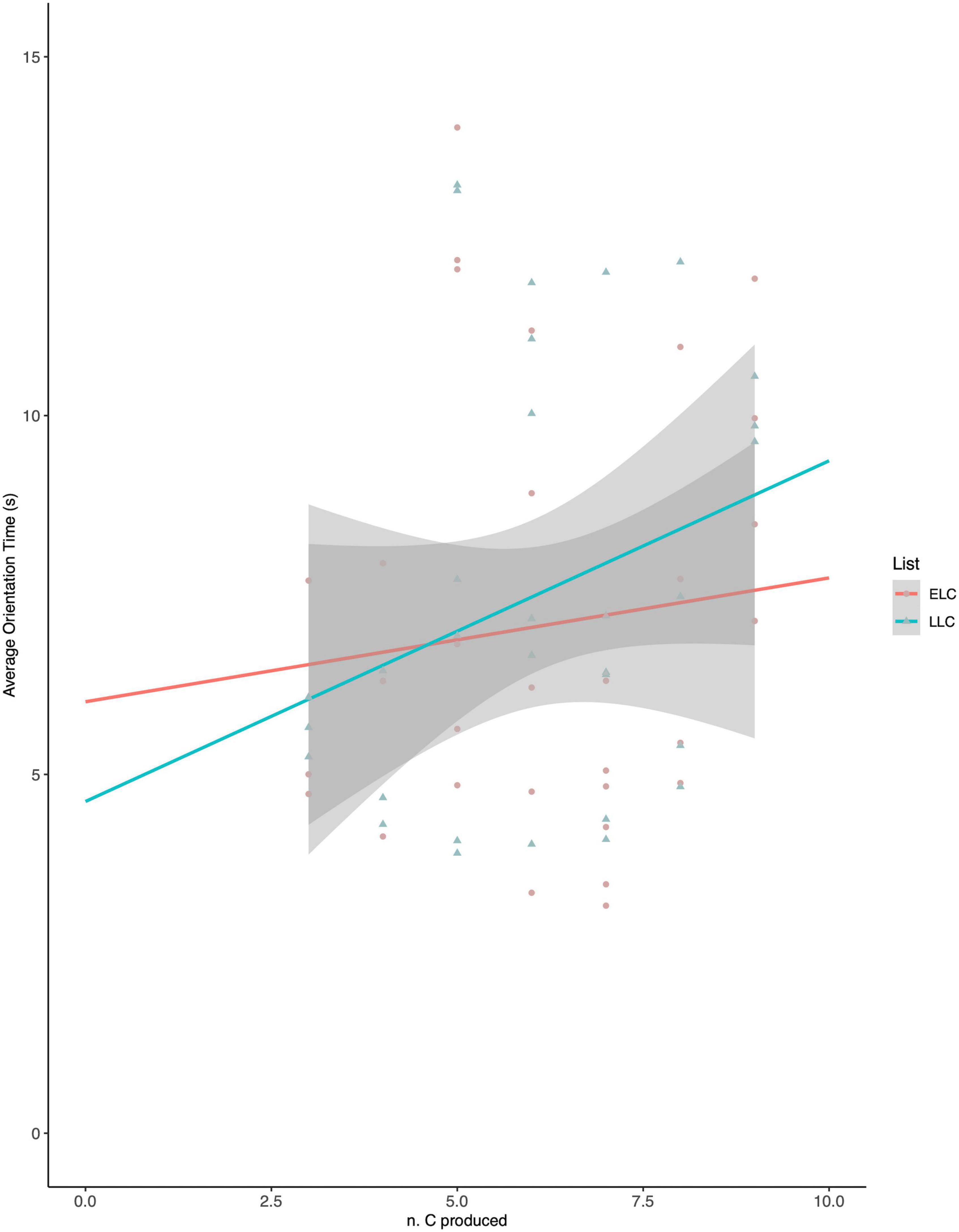
Frontiers | SSVEP BCI and Eye Tracking Use by Individuals With Late-Stage ALS and Visual Impairments

Applied Sciences | Free Full-Text | Design of OCC Indoor Positioning System Based on Flat Panel Light and Angle Sensor Assistance
GitHub - jimywork/shodanwave: Shodanwave is a tool for exploring and obtaining information from Netwave IP Camera.

Maximising security and compliance features from Microsoft 365 E5 license - 22 November 2022 | Local Government Association

Mathematics | Free Full-Text | Product Selection Considering Multiple Consumers’ Expectations and Online Reviews: A Method Based on Intuitionistic Fuzzy Soft Sets and TODIM
GitHub - DictionaryHouse/wordlist_RDP: Collection of some common wordlists such as RDP password, user name list, ssh password wordlist for brute force. IP Cameras Default Passwords.

GigE Vision® Device IP Package (1GbE version/10GbE version) (Discontinued) - Semiconductor Business -Macnica,Inc.

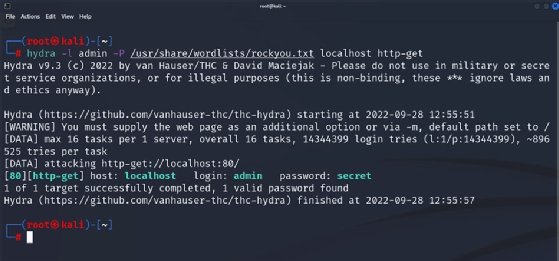





/Academy-The-top-password-cracking-techniques-used-by-hackers-Hero.jpg?width=1200&name=Academy-The-top-password-cracking-techniques-used-by-hackers-Hero.jpg)